Node.js Security Working Group AMA Recap
Members of the Node.js Security Working Group recently answered questions regarding what their group does, and how the security of Node.js can be improved.
Node.js Security Working Group AMA Recap
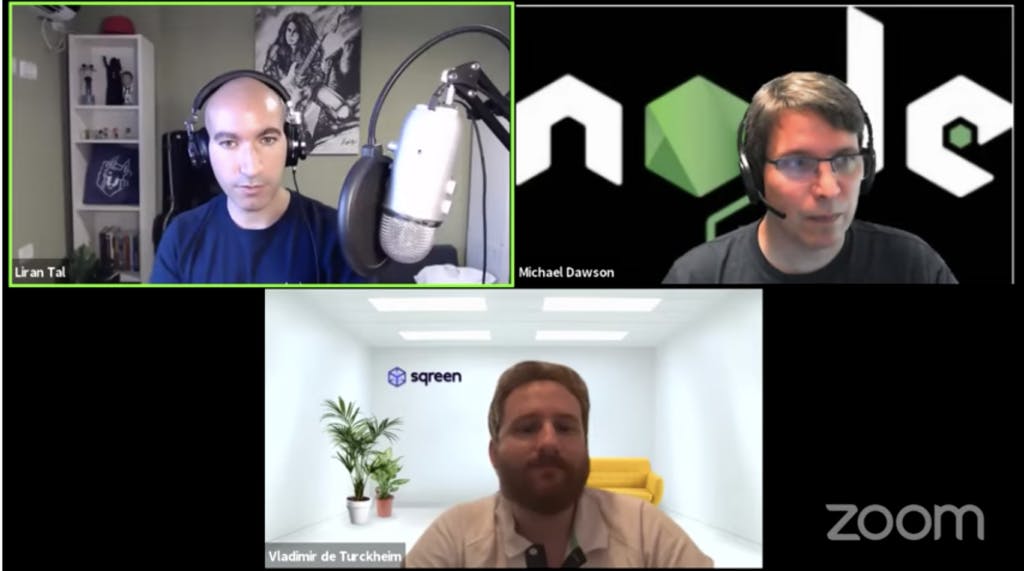
Members of the Node.js Security Working Group recently answered questions regarding what their group does, and how the security of Node.js can be improved. The Node.js Security Working Group is a community driven project that investigates security reports to reduce the vulnerability of the Node.js ecosystem. Liran Tal, a senior developer advocate at Snyk served as the moderator for the AMA series. Vladimir de Turckheim, a developer at Sqreen, and Michael Dawson, IBM community lead for Node.js, answered questions and discussed topics posed by viewers of the live stream.
Full panel discussion available here
The content of the AMA generally fell into two categories: a discussion of how the Security Working Group functions or a response to a viewer’s security concern. The talk began with a discussion of “bug bounties” — monetary rewards given to developers who report potential security vulnerabilities in the Node.js ecosystem. Dawson and Turckheim discussed problems with this system, challenges that the working group has faced and the future of the group in a changing landscape.
Dawson and Turckheim also addressed security concerns that viewers of the live stream had. The questions spanned a wide range of topics, from identifying security risks to using https to protect online data. Finally, the members of the panel reviewed how people can join working groups. They admitted that working groups take up a lot of time, but are a good way to give back to the community, and meet people who share similar interests.
A summary of the video is available below:
Panel starts 0:25
Member introductions 1:33
What is the Node.js Security Working Group? 04:52
How the members got started, what current members do (Vladimir) 10:18
Bug Bounties 12:13
Where can you find the Security Working Group? 14:43
How Bug Bounties can create tension 15:21
Potential alterations to the Bug Bounty system 19:19
How to roll out a patch to the Node.js ecosystem 23:04
Challenges that the Security Working Group faces 24:19
Interactions with the OpenJS and larger Node.js community 33:58
Using pattern searches to detect security issues early 40:09
How to secure JSON data transmissions 43:30
Should a best practice security guide be created? 46:50
Are malicious modules as common as they used to be? 50:30
How to tell between unintended bugs and malicious modules 53:35
Closing thoughts 55:28