Node.js Security Progress Report – Progress on Permission Model, Fuzzer and Connections with Community
Check out what we've been up to in this edition of our Node.js Security Progress Report.

Last month, there was excellent progress on the Node.js Permission Model, which is being used more in the community, exactly our goal. There’s also a new initiative to get the Node.js fuzzer up and running. This is based on the OSS-Fuzz project and supported by OSTIF. We also reached out to new communities at the Open Source Experience show in Paris talking about how you don’t need to be an expert to get involved in Node.js security. More details below.
The Open Source Security Foundation (OpenSSF) Project Alpha-Omega support has been critical in helping strengthen Node.js security practices. Thank you!
Fix and Triage Security Issues
7 reports were submitted in December.
- 2 New
- 1 Triaged
- 2 Non applicable
- 2 Informative
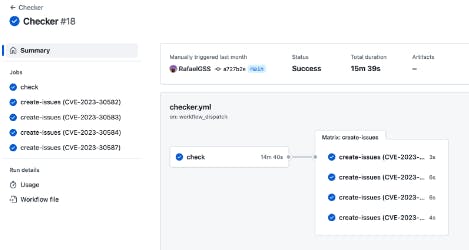
To handle the issue that some CVEs were identified as unpublished in the National Vulnerability Database (NVD) the Node.js team created a repository to track all CVEs published by the Node.js team. After every security release, we proactively check if the CVEs were published. Repo is available here: https://github.com/RafaelGSS/nodejs-cve-checker
Node.js Security Team Initiatives
The current Security Working Group Initiatives are: Permission Model, 2 Phase, Auditing the Build Process of Dependencies Automating update dependencies (done), Assessment against best practices, and Automating Security release process.
In December there was significant work done on the Permission Model, including fixing compatibility with Electron. Updates are in the documentation. For addons, native addons are restricted by default, but it’s also possible to add an --allow-addons flag. And we’ve added tests to URL paths. The Permission Model will soon (after Node.js 21.6.0) accept relative paths through the CLI. For example: --experimental-permission --allow-fs-read=./index.js. This is based on requests from the community.
Permission Model roadmap information is available here, and includes a discussion in December about addons.
In the Threat Model, we’ve clarified that some parts of WASI do not provide a security mechanism and therefore are outside of the Threat Model. WASI is a modular system interface for WebAssembly focused on security and portability.
And there is a new initiative from the Node.js Security Team for fuzzing Node.js. Fuzz testing or fuzzing is an automated software testing method that injects invalid, malformed, or unexpected inputs into a system to reveal software defects and vulnerabilities like buffer overflow. A fuzzing tool injects these inputs into the system and then monitors for exceptions such as crashes or information leakage.
This initiative is led by the Open Source Technology Improvement Fund (OSTIF) and the Node.js team will be working with David Korczynski, researcher at @AdaLogics. David did the initial work for getting Node into OSS-Fuzz. There are currently two projects integrated into OSS-Fuzz which are targeting code of nodejs:
Nodejs: https://github.com/google/oss-fuzz/tree/master/projects/nodejs
llhttp: https://github.com/google/oss-fuzz/tree/master/projects/llhttp
The initial goals are to first get the Node.js project up and running and also to update the fuzzer and extend the setup.
Also in December, Microsoft joined a Security Working Group meeting to discuss integration of code integrity (policy mechanism) on Windows, and they have created a draft Pull Request. We had other participants as well. OSTIF joined as part of the fuzzing work. And SPDX discussed supporting SBOMs on Node.js. Previously, CycloneDX had joined to discuss SBOMs as well. It’s important that the SBOMs are sustainable. Node.js is looking at different solutions to guarantee SBOM support into the future.
Node.js Security Sustainability
On December 6, Rafael Gonzaga delivered a talk called “5 Ways You Could Have Hacked Node.js” at the large Open Source Experience show in Paris. It was a great event with a lot of people from different communities participating! Rafael’s talk focused on the technical aspects of hacking and securing Node.js and covering the tactics used by the Node.js team to deal with vulnerabilities. The talk also covered how you can earn money by finding critical vulnerabilities in Node.js. The topic was for developers, security enthusiasts, or people curious about Node.js security.
Get Involved
Interested in getting involved with Node.js security? We are actively looking for new contributors! Find out more about the Node.js Security Team here: https://github.com/nodejs/security-wg
If you want to join in help Node.js, contributions are welcome. There are multiple ways and places you can contribute: https://nodejs.org/en/get-involved/contribute If you want to jump right here, here’s information on creating a Pull Request: https://github.com/nodejs/node/blob/main/CONTRIBUTING.md
The Node.js First Contribution live stream have been held and are continuing through January 2024. If you’d like to participate, there will be both English and Portuguese channels available. Please join!